The OLOID Blog
Articles and Podcasts on Customer Service, AI and Automation, Product, and more

Featured
Adaptive SSO: Benefits, Limitations, and Where It Falls Short
Adaptive SSO enhances traditional single sign-on by introducing contextual and risk-based decision-making into authentication workflows. Instead of relying on a one-time login, it evaluates factors such as device, location, and user behavior to determine whether access should be granted, challenged, or blocked. This approach improves access control while reducing unnecessary authentication friction. However, adaptive SSO still depends on assumptions about device trust and session continuity, which may not hold in environments with shared systems or dynamic user behavior.

Adaptive MFA Explained: How It Works and Why It Fails in Shared Environments
Adaptive multi-factor authentication adjusts authentication requirements based on risk, context, and user behavior to ensure stronger authentication without adding unnecessary friction for users. Instead of relying on static rules, it evaluates each authentication attempt in real-time and dynamically applies additional authentication steps only when needed. This approach helps verify a user’s identity more accurately while maintaining security and convenience across environments. As identity becomes more fluid, adaptive MFA enhances how organizations balance security requirements and user experience.

What Is Just-in-Time (JIT) Access? A Complete Guide
Just-in-time access ensures that user access is granted only when needed, instead of relying on permanent access that stays active unnecessarily. It replaces traditional access control methods by introducing time access and moving toward zero standing access across systems. With JIT access, users request temporary access to specific resources such as access to production or other sensitive systems. Access is approved based on defined access control policies and is automatically revoked once the task is completed. This approach helps reduce unnecessary access and minimizes the risk of unauthorized access to privileged accounts.

What is Just-in-Time Provisioning? How It Works & When to Use It
Just-in-time provisioning is a modern approach to user account creation that eliminates delays by provisioning users at login instead of in advance. It relies on identity providers and SSO workflows to assign access instantly based on real-time identity data. While JIT provisioning improves onboarding speed and reduces IT workload, it does not handle the full identity lifecycle. Organizations often combine it with SCIM provisioning to manage updates and deprovisioning.

Healthcare's Future in AI era Starts with Identity
ViVE showcased healthcare's AI ambition. HIMSS sharpened the urgency. And the Stryker cyberattack reminded the industry that innovation only scales when the trust layer underneath it is resilient.

Passkeys vs Passwords: What’s the Difference and Why It Matters
Passkeys vs Passwords explores how authentication is evolving from traditional password-based systems to modern, passwordless approaches. While passwords rely on shared secrets and user behavior, passkeys use public key cryptography and device-based authentication to verify identity securely. This shift reduces risks like phishing, credential theft, and password reuse, while improving login experience. As adoption grows, organizations are evaluating how passkeys fit into zero trust architectures and shared-device environments.

What is Passkey Authentication? How Passkeys Work and Why They Matter
Passkey Authentication is a passwordless authentication method that replaces traditional passwords with cryptographic credentials stored on trusted devices. Instead of relying on memorized passwords, passkeys use public-key cryptography and device verification, often through biometrics such as fingerprints or facial recognition. Because the private key never leaves the user’s device, passkeys reduce the risks of phishing, credential theft, and password reuse attacks.

What is Least Privilege Access? Definition, Benefits, and Implementation
Least privilege access is a security principle that ensures users, applications, and systems receive only the minimum permissions required to perform their tasks. By limiting unnecessary access rights, organizations reduce their attack surface and lower the risk of privilege misuse or credential compromise. The approach helps prevent attackers from escalating privileges or moving laterally across systems after a breach. Least privilege is also a foundational component of modern zero trust security and identity access management strategies.
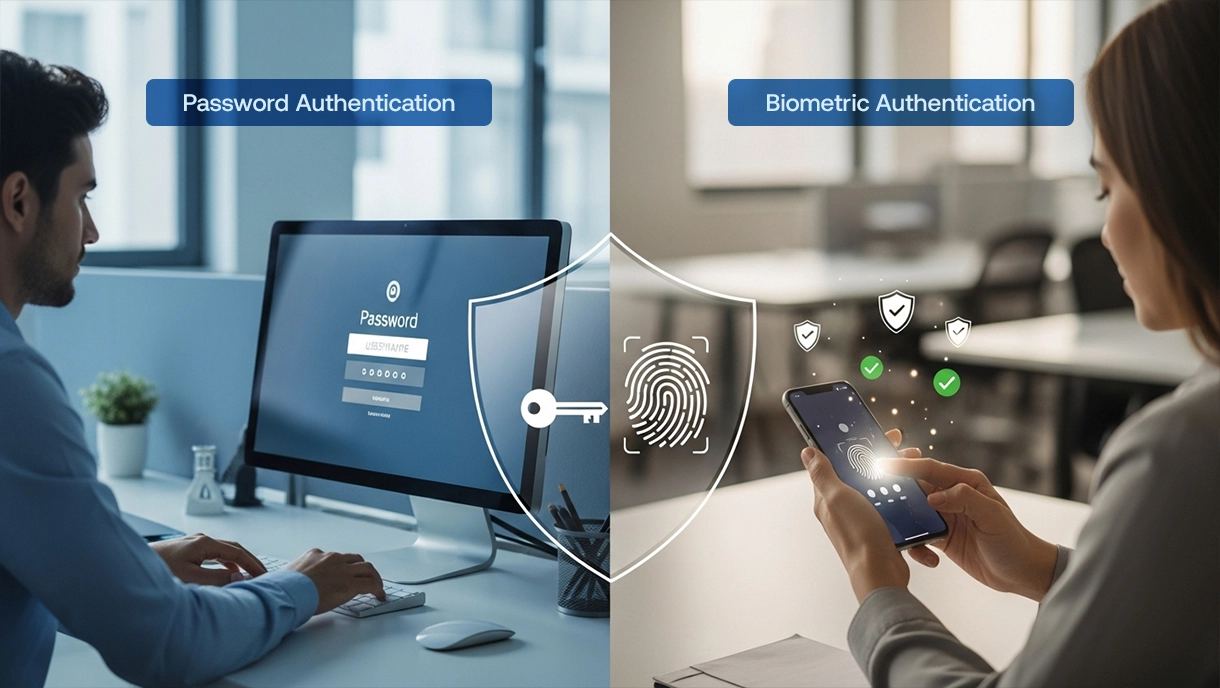
Password vs Biometrics: Which Authentication Method is More Secure?
Passwords rely on knowledge-based authentication, while biometrics verify identity using unique physical traits such as fingerprints or facial recognition. Although biometrics offer stronger resistance to phishing and credential theft, passwords remain widely used due to legacy system compatibility and ease of deployment. Modern enterprises increasingly combine biometrics with passwordless authentication and device trust to strengthen zero-trust security, particularly in shared device and frontline environments where traditional authentication models fall short.
-vs-Federation--A-Complete-Guide.webp)
Single Sign-On (SSO) vs. Federation: A Complete Guide
SSO and Federated Identity Management are foundational to modern identity and access management. SSO simplifies access within a single organization, while federation enables secure authentication across domains using standards such as SAML and OpenID Connect. However, shared-device and frontline environments introduce identity risks that traditional models were not designed to address. Extending identity enforcement to operational endpoints strengthens Zero Trust security without disrupting workflow.
1.webp)
What is Cloud Identity and Access Management (IAM)? A Complete Guide
Cloud identity and access management plays a central role in modern cloud security by verifying identities and controlling access across cloud environments. As enterprises adopt more cloud services, a well-designed IAM system enhances security through role-based access control, lifecycle management, and continuous monitoring while closing gaps in identities and access across frontline and shared environments.
.webp)
What is Zero Trust Network Access? A Complete Guide for Modern Enterprises
This guide explains Zero Trust Network Access (ZTNA), why traditional VPN-based security falls short, and how identity-driven access works in modern enterprises. It walks through ZTNA architecture, core principles, deployment models, and real-world use cases. The article highlights how ZTNA limits lateral movement and secures remote, cloud, and shared environments. It also shows how OLOID strengthens Zero Trust in shared workstation scenarios with continuous identity assurance.

SAML vs SSO: Key Differences and How Enterprises Implement Single Sign-On
This article clarifies the distinction between SAML and SSO in modern enterprise identity architecture, explaining how SSO defines the authentication strategy while SAML enables secure identity federation between identity providers and applications. Rather than treating them as competing technologies, it shows how they work together in hybrid environments and where SAML-based SSO remains most effective. It also explores where newer protocols fit and how enterprises design multi-protocol identity frameworks.

SAML Authentication Explained: How It Works, Benefits, and Enterprise Use Cases
SAML remains a backbone for enterprise authentication, enabling secure workforce access and browser-based Single Sign-On across business applications. The article explains how SAML works through Identity Providers, Service Providers, and assertions, showing why organizations still rely on it for stable identity operations. It presents SAML as relevant today, balancing where it performs strongly and where newer identity models may work better. The piece places SAML within the modern identity landscape alongside zero trust, passwordless authentication, and identity orchestration.

Digital Identity Verification: A Complete Guide to Remote Identity Proofing
Digital Identity Verification enables organizations to confirm user identities remotely without physical presence or passwords. Businesses implement this technology to prevent fraud, accelerate onboarding, and meet global KYC/AML compliance requirements. This guide explores verification methods, implementation strategies, real-world applications, and best practices for success. Compliance officers, fintech executives, and security teams gain actionable frameworks for deploying robust identity verification across digital channels.

What is SCIM? The Complete Guide to System for Cross-domain Identity Management
SCIM, or System for Cross-domain Identity Management, is an open standard protocol that automates user provisioning and deprovisioning across cloud applications. This blog explains how SCIM eliminates manual identity management tasks, reduces security risks, and streamlines employee lifecycle workflows. Learn the implementation strategies, real-world use cases, solutions to common challenges, and best practices for deploying SCIM effectively in your organization.

FIDO2 WebAuthn: The Complete Guide to Passwordless Authentication
FIDO2 WebAuthn transforms digital security by eliminating traditional password vulnerabilities. This comprehensive guide explores what FIDO2 and WebAuthn are, how they work together, and why organizations are adopting them. Explore the technical architecture, step-by-step registration and authentication flows, implementation strategies, and real-world use cases.

Federated Identity Management: Complete Guide to Secure Cross-Domain Authentication
Federated Identity Management enables secure authentication across multiple organizations without creating separate accounts for each system. This blog explores how FIM works, key protocols like SAML and OAuth, implementation steps, real-world use cases, and best practices. Learn how enterprises use federation to reduce password fatigue, enhance security, and streamline access across cloud applications and partner ecosystems.
Federated SSO: Enabling Seamless Cross-Organizational Authentication
Federated Single Sign-On (SSO) enables seamless authentication across multiple organizations through trusted identity federation relationships. This comprehensive guide explores the fundamentals of Federated SSO, how it differs from standard SSO, and the protocols that enable cross-domain access. IT administrators, enterprise architects, B2B SaaS companies, and security professionals will find step-by-step implementation guidance, solutions to common challenges, best practices for secure federation, and real-world use cases.

What Is Context-Based Authentication? Benefits, Use Cases & How It Works
Context-based authentication evaluates environmental and behavioral factors before granting system access. Traditional authentication applies identical requirements regardless of access circumstances or risk levels. This guide explains how context-aware authentication works, analyzes signals like location and device health, and enforces dynamic policies. Learn implementation strategies, real-world use cases, and best practices for deploying intelligent authentication.

Fingerprint Authentication Explained: How It Works, Benefits, and Real World Applications
Fingerprint authentication uses unique biological patterns to securely and conveniently verify user identity. This comprehensive guide explores fingerprint scanning, including how it works, different sensor types, implementation strategies, and practical applications. Learn the advantages of biometric verification, common challenges with proven solutions, and best practices for deploying this technology. Whether you're evaluating security options or implementing access systems, this resource provides actionable insights for modern authentication needs.

What is Authentication? Your Complete Guide to Digital Identity Verification
Authentication forms the foundation of digital security by verifying identity before granting system access. This comprehensive guide explains authentication fundamentals, the verification process, and the three primary authentication factors. Readers will discover various authentication methods from passwords to biometrics, understand the critical difference between authentication and authorization, explore real-world use cases, and learn proven security best practices. Whether you're an IT professional, business leader, developer, or general user interested in digital security, this resource provides precise, actionable knowledge for understanding and implementing effective authentication strategies.

Behavioral Biometrics: The Future of Continuous, Passwordless Authentication
Behavioral biometrics represents the future of fraud prevention and continuous authentication technology. This comprehensive guide explores how AI and machine learning analyze unique user behavior patterns to detect fraud, prevent account takeover, and enhance security without adding friction. Learn about behavioral biometrics types, technology fundamentals, real-world applications across industries, implementation best practices, and emerging trends.
What is SSPR: Benefits, Implementation, and Security Considerations
Self-Service Password Reset (SSPR) empowers users to reset passwords and unlock accounts independently without IT helpdesk intervention. This comprehensive implementation guide covers SSPR fundamentals, step-by-step deployment in cloud and hybrid environments, authentication methods, security considerations, and proven strategies to maximize user adoption. Get actionable insights to reduce support costs, enhance productivity, and strengthen security postures.
.webp)
3FA (Three-Factor Authentication): The Ultimate Guide to Maximum Security
Three-Factor Authentication represents the pinnacle of identity verification security in today's threat landscape. This comprehensive guide explores how 3FA combines knowledge factors, possession factors, and biometric factors to protect sensitive data from unauthorized access. Learn the detailed implementation strategies, proven deployment best practices, industry-specific real-world applications, and practical solutions to common challenges.

Time-Based One-Time Password (TOTP): The Complete Guide to Secure Authentication
Time-Based One-Time Password (TOTP) generates temporary authentication codes that expire within 30-60 seconds. Organizations use TOTP to secure access without relying on vulnerable SMS-based verification methods. This guide explains technical implementation, security advantages, and deployment strategies for enterprise environments.

Biometric Spoofing Explained: Risks, Real Attacks and Prevention
Biometric spoofing uses fake fingerprints, facial replicas, or synthetic voice recordings to deceive authentication systems. Attackers exploit weaknesses in biometric sensors and verification algorithms to bypass security without legitimate credentials. This guide explains spoofing techniques, real-world attack examples, and comprehensive defense strategies. Learn about liveness detection technologies, multi-factor authentication approaches, and best practices for preventing biometric authentication compromise across enterprise environments.

Rainbow Table Attacks: What They Are, How They Work, and How to Protect Passwords
Rainbow table attacks use precomputed hash databases to crack passwords rapidly by matching stolen hashes against precalculated values. These lookup tables exploit unsalted password hashes through time-memory tradeoff techniques, avoiding repeated hash calculations. This guide explains how rainbow tables work, why they remain effective, and provides comprehensive defense strategies. You'll discover modern hashing algorithms, salting techniques, and authentication methods that make rainbow table attacks computationally infeasible.

Password Spraying: What It Is, How It Works, and How to Defend Against It
Password spraying is a credential-based attack in which attackers try common passwords across multiple user accounts simultaneously. Unlike brute-force attacks targeting a single account, password spraying distributes attempts to avoid lockout mechanisms. This guide explains how password spraying works, why it succeeds, and provides detection strategies. You'll discover best practices for prevention, including multi-factor authentication, risk-based policies, and passwordless alternatives, eliminating password vulnerabilities.

What Is a Physical Security Key? How It Works, Why It Matters & When to Use It
Physical security keys are hardware devices that provide cryptographic authentication and resist phishing and credential theft attacks. These tamper-resistant tokens use FIDO2 and WebAuthn protocols, replacing passwords with device-bound verification. This blog explains how security keys work, compares types, and provides implementation guidance. Explore use cases, setup procedures, and considerations for deploying hardware authentication across personal and enterprise environments.

Mobile Authentication Explained: Methods, Benefits, and Secure Login Best Practices
Mobile authentication uses smartphones as primary verification devices, replacing traditional password-based login systems. Organizations deploy biometrics, passkeys, push notifications, and device-bound credentials for secure access. This blog explains how mobile authentication works, compares security methods, and provides implementation strategies. Learn the best practices, use case recommendations, and security considerations for deploying mobile-first authentication across enterprise environments.
Making every day-in-the-life of frontline workers frictionless & secure!
Get the latest updates! Subscribe now!
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.



